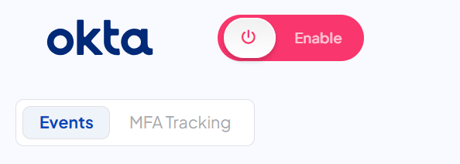
Enabling the Okta integration
How to enable the Okta integration
Permissions
- MFA tracking - okta.users.read and Read-only admin role
- Phishing sim - okta.users.manage and Organization admin role
Steps
- Click into your integrations tab
- Select the "Okta" integration
- Click the "Enable" toggle
- A new window should pop up with the Okta set-up wizard
- Follow the steps on the wizard, or refer to the rest of this guide as the same steps will be posted below
Application
-
Open your Okta Admin Console and go to Applications > Applications

- Click "Create App Integration"
- Choose "API Services" and click "Next"

-
Fill in the App integration name as:
CultureAI Api Integrationand click "Save".
Configure
- Click "Edit" on the "Client Credentials" section.

- Change the "Client authentication" method to "Public key / Private key" and click "Add Key"

- Click "Generate new key"

-
Click "PEM" to get the key in PEM format, and take a copy of the private key, store this securely, you will not have another opportunity to retrieve this key and click "Done"

- Click "Save"
- Click "Edit" on the "General Settings" section.

-
Uncheck "Require Demonstrating Proof of Possession (DPoP) header in token requests" and click "Save".

Scopes
- Change to the "Okta API Scopes" tab

- Click "Grant" on "okta.users.read" NOTE: The integration will fail to enable if this is missing
- Click "Grant Access"

Privilege
- Change to the "Admin Roles" tab and click "Edit assignments"

- Select the "Read-only Administrator" from the left dropdown, and click "Save Changes"

Authentication
Please provide the following information and fill them out in the wizard
Click the "Authenticate with Okta" button
You're done!